Every Enterprise Is Unique. Your Risk Decisions
Should Reflect That.
Empirical builds data-driven models to prioritize, remediate, and summarize cybersecurity findings. We’re building the world’s first organization specific models for cybersecurity.
Our Models
CloseEmpirical Local Models
Your enterprise has environmental and telemetry data that should be used in decision making. Empirical unlocks the value of these datasets by training a local model, specific to you and only accessible by you, to support your enterprise’s decision making.
Empirical Global Models
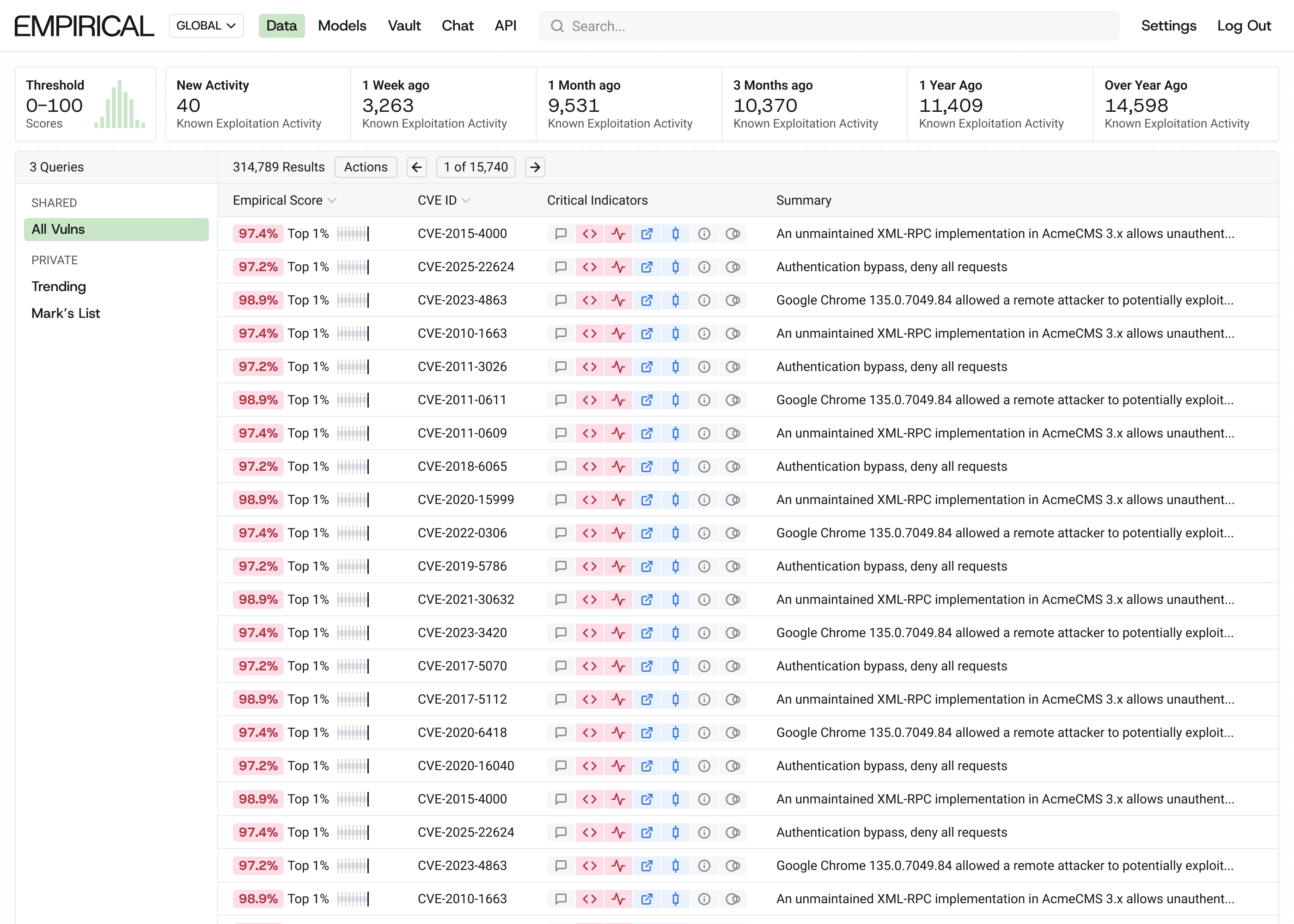
Global models combine real-time internet exploitation telemetry with EPSS predictions to provide the most accurate view of exploitation. It monitors activity over 17,000 known exploited in the wild CVEs, and uses that data in the model. This is 12x DHS CISA’s KEV, and far more than any other vendor out there.
EPSS Model
EPSS provides a prediction of the probability of exploitation of a vulnerability. It uses data contributed by participating vendors and is the free and open model used by over 120 vendors to score vulnerabilities. Empirical maintains and trains the model.
How It Works
Our platform supports Empirical's global and local models. The global model, trained on ~2 million exploitation events, captures attacker behavior across the internet. Local models, trained on your environment's telemetry, capture more targeted attacks. The two models work together to surface the vulnerabilities most likely to be exploited in your infrastructure.
Effort, Coverage, and Efficiency
CloseAll Published Vulns (CVEs we could prioritize)
Effort
Measures the relative workload as the proportion of vulnerabilities prioritized out of all the possible CVEs:
Correctly Prioritized + Incorrectly Prioritized / Everything
Efficiency
Measures how accurately our strategy focuses on vulnerabilities that have exploitation activity:
Correctly Prioritized / Correctly Prioritized + Incorrectly Prioritized
Coverage
Measures how well our strategy covers the vulnerabilities we prioritized from all vulnerabilities that show exploitation activity:
Correctly Prioritized / Correctly Prioritized + Incorrectly Ignored
Why security teams choose Empirical
A common language for risk decisions
The Empirical global model grounds every prioritization decision in observable evidence. When someone asks "why are we fixing this one first?" The answer is a probability backed by real world exploitation telemetry, with critical indicators explaining the logic in real time.
Your context changes the answer
A critical vulnerability behind a WAF with no internet exposure is not the same risk as a medium CVE on an unpatched, public-facing server running your payments stack. Generic models can't tell the difference. Our local model can because it trains on data only your environment produces.
We predict which vulnerabilities will be exploited in your environment.
CVSS measures severity, and EPSS predicts global exploitation probability, but neither tells you what will be exploited in your environment next month. Our models answer this crucial question. We demonstrate higher coverage and efficiency than traditional methods or off the shelf models. When fixing a limited set of vulnerabilities our predictions catch more of what actually gets exploited and waste less effort on what doesn't. We publish the data to prove our performance.
Our Products
Local Models
Local models are trained on your environmental and telemetry data to support your enterprise’s decision making.
Global Models
Global models combine real-time exploitation telemetry with EPSS predictions to accurately depict exploitation.
EPSS Model
Empirical builds and maintains the world’s only public machine learning model in cybersecurity, EPSS.